The world of cybersecurity is fraught with constant challenges and evolving threats. Among these, the term 0day onion has emerged as a critical concept that signifies both vulnerabilities and the underground activities surrounding them. This article delves into the intricacies of 0day onion, exploring its implications for cybersecurity and the dark web.
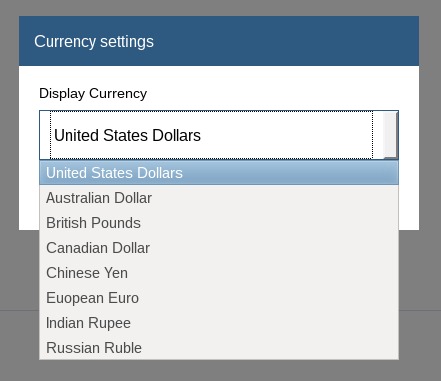
That is why in 2006 they created "the most private search engine in the world", which does not record, track, or share your personal data. On the other hand, we have Tor2Web, which is a service that helps people who are not yet in the Tor network. Ahmia developers believe that the Tor network is an important distributed platform to protect anonymity and privacy around the world. At the moment they are making minor improvements to the search engine and working on the Beta version of their new link directory.
The Tor network provides the anonymity by routing traffic through multiple relays, hiding the service’s physical IP address. CVEs and exploits are highly sought after by black hats and security professionals alike. For the time being, please go to this pastebin where I will import the .onion links I saved in the pastebin to here over time. But it clearly demonstrates that even the most notorious ransomware groups are not immune to the same cyber vulnerabilities they exploit — and that the walls are closing in. EDB and 0day.today both contain tens of thousands of exploits, and although there is a good amount of overlap between the projects, they each offer their own unique exploits.
So add ignoring security guidance to the list above, and, well, I’m suspicious. Also, the Spring documentation is clear about security implications of YOLO usage of DataBinder. The vulnerability allows a remote attacker to execute arbitrary code on the target system. Also called intermediate varieties, these onions can be spring or fall-planted depending on how mild your winters are.
- George is a seasoned Cybersecurity writer who has been writing guides and news about digital security for over five years.
- Bloomberg has published a profile on Chapman, her story, and her motives.
- Attackers use specialized tools to perform port scanning and service fingerprinting against the Tor network, looking for open ports running outdated or poorly secured software.
- Vulners, founded by Kir Ermakov, is a CVE database currently containing over 176,500 indexed exploits.
- On the dark web, appearance can be deceiving, and often, it’s designed that way on purpose.
0day Onion
The term 0day refers to a software vulnerability that is unknown to the vendor and, therefore, has no patch available for it yet. Cybercriminals often exploit these 0day vulnerabilities to carry out attacks. When combined with the concept of the onion routing system known as Tor, we enter a realm where these vulnerabilities can be traded, purchased, or auctioned off on dark web marketplaces.
Understanding 0day Onion Markets
0day onion markets operate in the convoluted layers of anonymity provided by Tor. Here, malicious actors can exchange sensitive information without revealing their identities. These markets can be thought of as a digital black market for hackers, where the most sought-after exploits are sold at high prices due to their potential impact.

The anonymity of 0day onion markets attracts not just hackers but also individuals and organizations looking to bolster their cybersecurity defenses. Companies may seek information about 0day vulnerabilities to proactively address potential threats, making these markets a double-edged sword.
Risks and Mitigation Strategies
- The search engine has indexed over 400,000 pages, and you can ask it to match your exact search term.
- He posted stupid things in very public and monitored places and it only took a little research in the right places to put the pieces together.
- Unnecessary services provide additional vectors for a novel exploit to take hold, and their absence is a critical layer of defense against an unknown attack.
- Threat Actor Profiling
Organizations face significant risks when it comes to 0day onion exploits. If a critical vulnerability is discovered and exploited before it is patched, the effects can be devastating, including data breaches and financial loss. Therefore, recognizing the threat posed by 0day vulnerabilities is the first step toward mitigation.

To protect against the risks posed by 0day onion exploits, organizations should invest in robust cybersecurity measures, including:
- Regular Software Updates: Keeping systems up to date with the latest patches can minimize vulnerabilities.
- Intrusion Detection Systems: Implementing monitoring tools can help detect unusual activity indicative of an exploit attempt.
- Employee Training: Educating employees about security best practices can significantly reduce the risk of successful attacks.
The Future of 0day Onion Vulnerabilities
The landscape of 0day onion vulnerabilities is ever-changing. As technology evolves, so do the methods employed by cybercriminals. New vulnerabilities are constantly emerging, and the underground market will likely continue to adapt. Therefore, organizations must remain vigilant, continually evolving their cybersecurity strategies to counter these threats.
In conclusion, the 0day onion concept encapsulates the risks and opportunities presented by unknown software vulnerabilities. By understanding this interplay, organizations can better prepare themselves against the diverse and sophisticated threats in today’s digital age.