In the world of online privacy and the dark web, .onion links play a crucial role. These unique web addresses are part of the Tor network, a system designed to provide anonymity for both users and website operators. Unlike conventional websites, which operate over the surface web, .onion links allow users to access sites that are often hidden from standard search engines, thus adding a layer of security and privacy to online browsing.
onion Link
Accessing .onion links requires the use of the Tor Browser. This specialized browser routes your internet traffic through a series of volunteer-operated servers, ensuring that your IP address remains concealed. The anonymity afforded by .onion links has made them appealing for a variety of activities, some of which may be controversial or illegal. However, many sites using .onion addresses also provide valuable services, such as privacy-focused news outlets and forums where users can discuss sensitive subjects without fear of reprisal.
Many phishing sites imitate trusted platforms like the Hidden Wiki to trick users. Many fake platforms exist purely to steal funds, so only a few services are still active in 2025. Dark web sites use a different kind of domain — the .onion extension — which doesn’t work on regular browsers. The dark web, however, is a small, intentionally hidden part of the deep web that requires special tools like the Tor Browser to access.
- This .onion link makes it impossible for hackers to impersonate your profile.
- Therefore, use NordVPN to view search results and browse anonymously.
- This is also why the sites on the dark web are called Tor links.
- Onion sites, also known as onion sites, rely heavily on the Tor network to operate.
- Without these tools, neither Google nor any surface web browser can reach these secure, hidden parts of the internet.
- However, you should not see it as an opportunity to engage in illegal activities to avoid trouble with authorities.
The search results from DuckDuckGo will be for websites on the regular web, which you still visit through Tor. These nodes/relays and the websites operating on them make up the Tor network, or as it is more generally named, the dark web. Resources specifically curated for researchers studying privacy technologies, network security, and censorship resistance. We employ a multi-step verification process to ensure all listed onion services are legitimate and as described. With tools like Tor and .onion addressing, we can build—and browse—a more private, secure, and open internet. Since .onion sites don’t rely on public domain registrars or centralized hosting, they’re much harder to block or shut down.
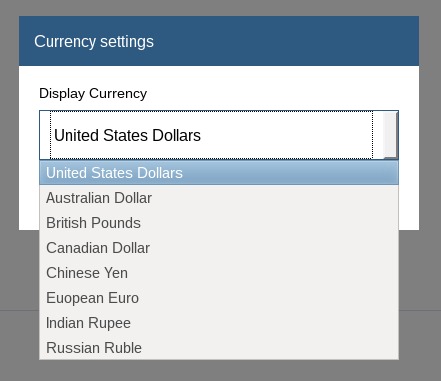
How to Access .onion Links
By design, .onion sites prevent third parties—including internet service providers, governments, or hackers—from tracking who visits them or what content is being accessed. While it’s safe to search for and scroll through dark web search engine links, websites in the results may harbor malware, disturbing content, or serve as gateways to scams. This means users can browse sensitive content, communicate securely, or access restricted services without fear of profiling or monitoring. Tor also supports hidden services (.onion websites) for added anonymity. Users can explore onion sites easily and search for content without having to know any specific onion links in advance. Privacy-focused internet users who access onion sites may see greater anonymity while browsing or sharing sensitive information.
To access a .onion link, installation of the Tor Browser is essential. Once that is complete, users can visit .onion addresses directly in the browser's address bar. This process keeps their browsing habits confidential, as the Tor network encrypts data multiple times before it reaches its destination. This makes it incredibly difficult for any outside parties to track user activity or determine their locations.

Benefits and Risks

The primary advantage of using .onion links is privacy. Users can browse and communicate without being monitored by government agencies or corporations. However, this anonymity can lead to risks. Some .onion links may lead to illegal content, scams, or malicious software. Caution is essential, as not all content found on the dark web is safe or legitimate.
Legitimate Uses of .onion Links
Despite their association with illegal activities, numerous legitimate websites operate under .onion links. These include secure email services, whistleblowing platforms, and forums for those living under oppressive regimes. For example, the famous leak platform WikiLeaks uses .onion links to provide a secure dropbox for sensitive documents. This illustrates the potential for .onion links to serve as a tool for free expression and resource sharing, particularly in environments where censorship is prevalent.
Conclusion
Understanding .onion links is vital for anyone interested in internet privacy and security. While they can connect users to a wealth of information and communities, caution should always be exercised. Recognizing the benefits and risks associated with .onion links helps users navigate the complex landscape of the dark web safely and effectively.